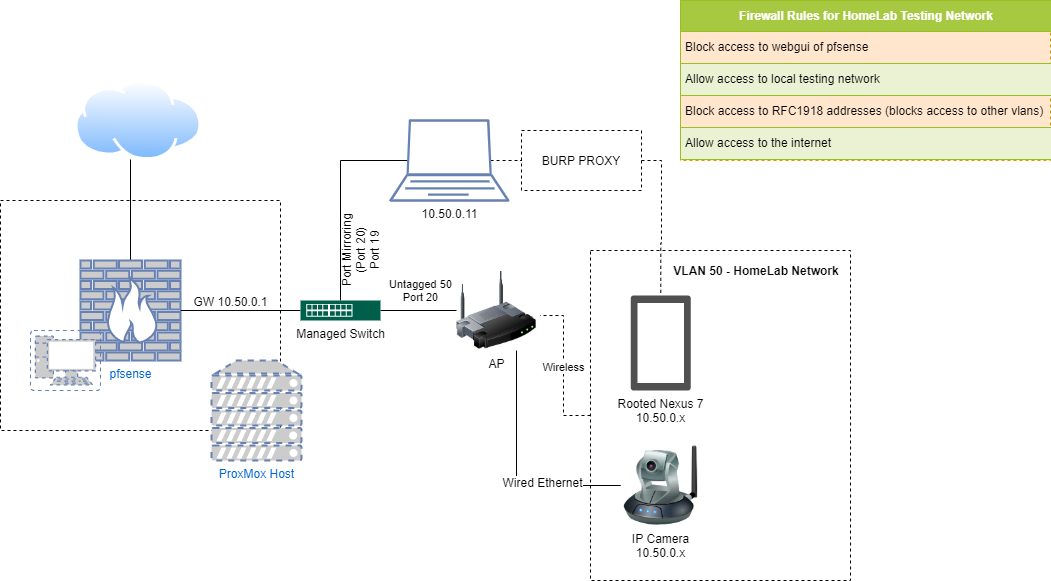
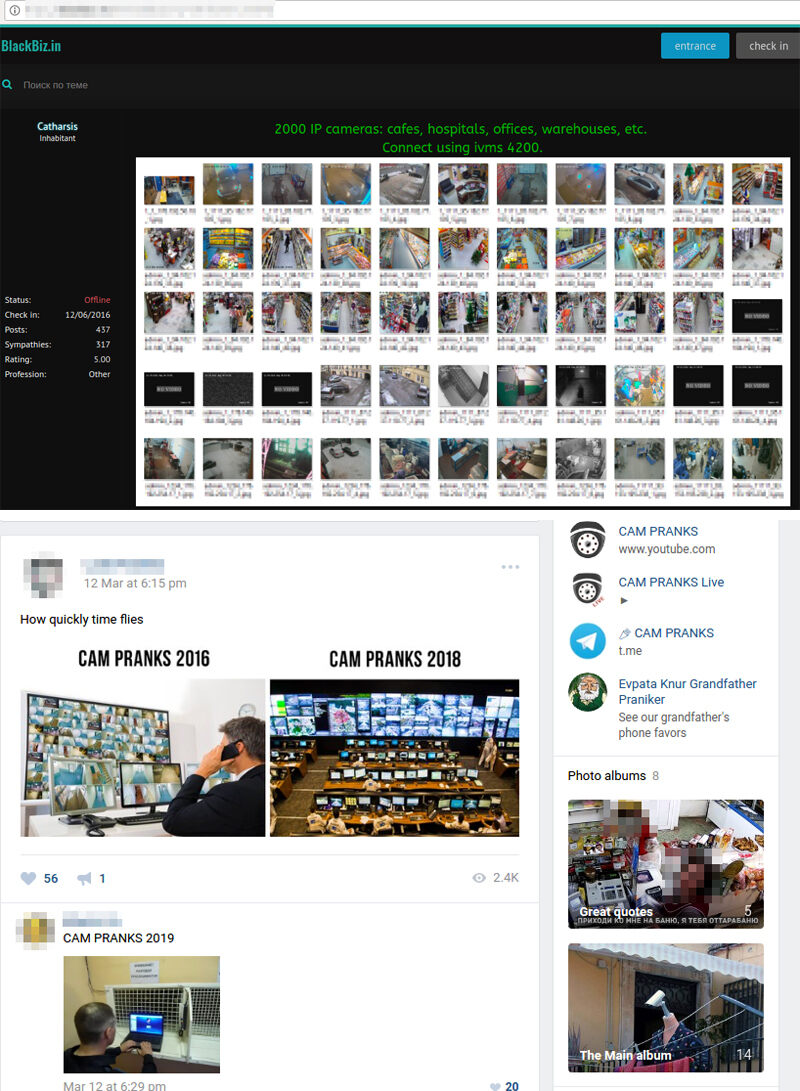
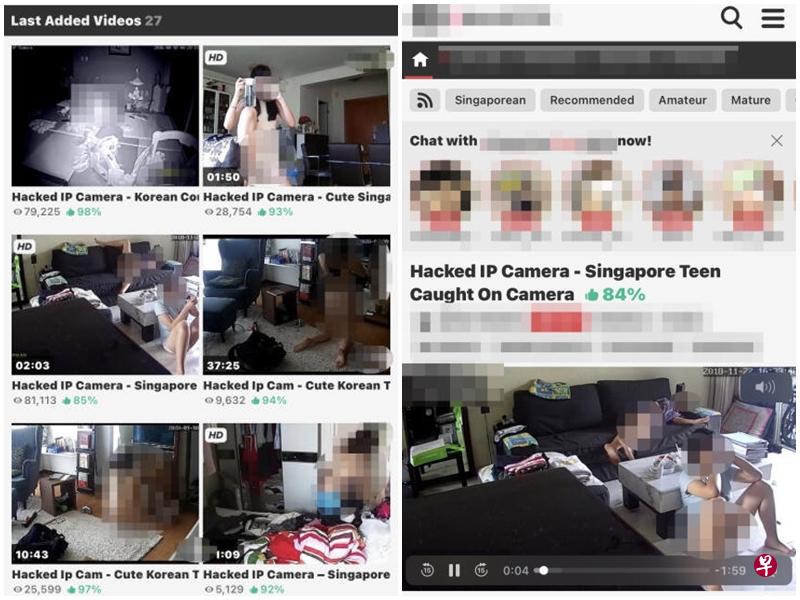
Exposed Video Streams: How Hackers Abuse Surveillance Cameras - Nouvelles de sécurité - Trend Micro FR

Is your webcam a Trojan Horse for hackers, voyeurs and spies? Hundreds of Hong Kong households seen by strangers online via Shodan search engine | South China Morning Post